Risk Assessment
Comprehensive risk assessment services that accurately identify and prioritise OT cyber security risks with actionable remediation recommendations.
Details 
OT Vulnerability Assessment
Baseline review of your OT environment security capabilities and weaknesses. Enables the mitigation of priority risks identified and the development of a long-term security strategy.
Details 
OT Asset Inventory
Comprehensive asset discovery services that result in a complete view of your OT assets, systems and networks. Enables risk exposure evaluation and obsolescence management.
Details 
Penetration Testing
We analyse attack vectors and non-disruptively test egress and ingress points to and from your OT systems and networks. Provides insight into operational impacts from a cyber compromise.
Details 
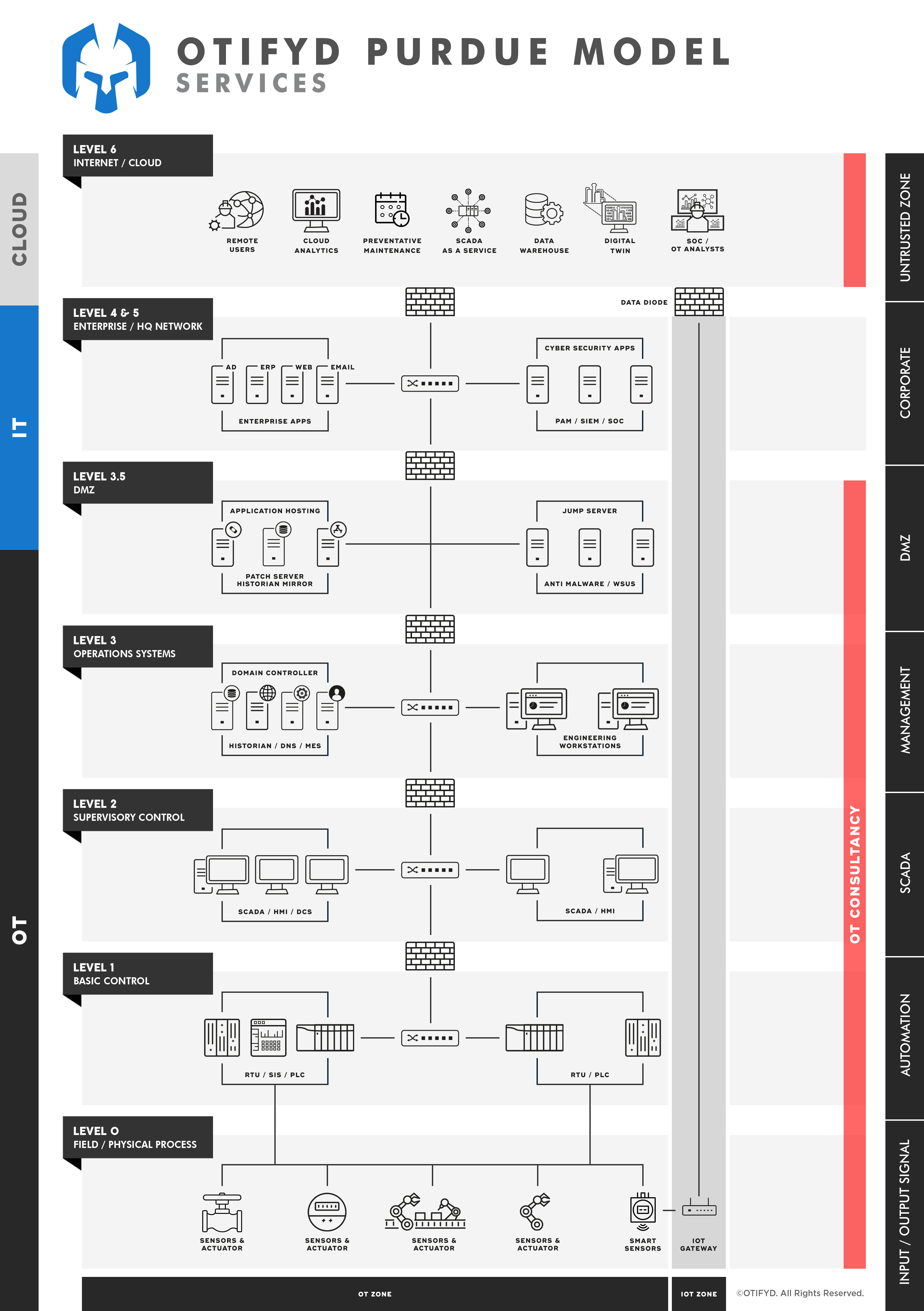
Architecture Assessment
Technical assessment of an architecture where current security posture is considered, and any improvements identified. The focus is on establishing a defendable architecture.
Details 
Regulatory Compliance
We support organisations in successfully navigating this evolving and complex space. Our guidance helps you become and remain compliant.
Details